- (02) 6009 5112
- [email protected]
- Mon-Fri 8:30 - 5:30
HaveComprehensiveCyber Security Services
Boost your business resilience and customer trust with a Techcellence managed security service. We leverage industry-leading tools and insights to provide you with a secure digital environment.
Build Customer Trust
Security isn’t static. Once your defences are up, each cyber threat evolves.
As cyber risks rise, we counter them head on.
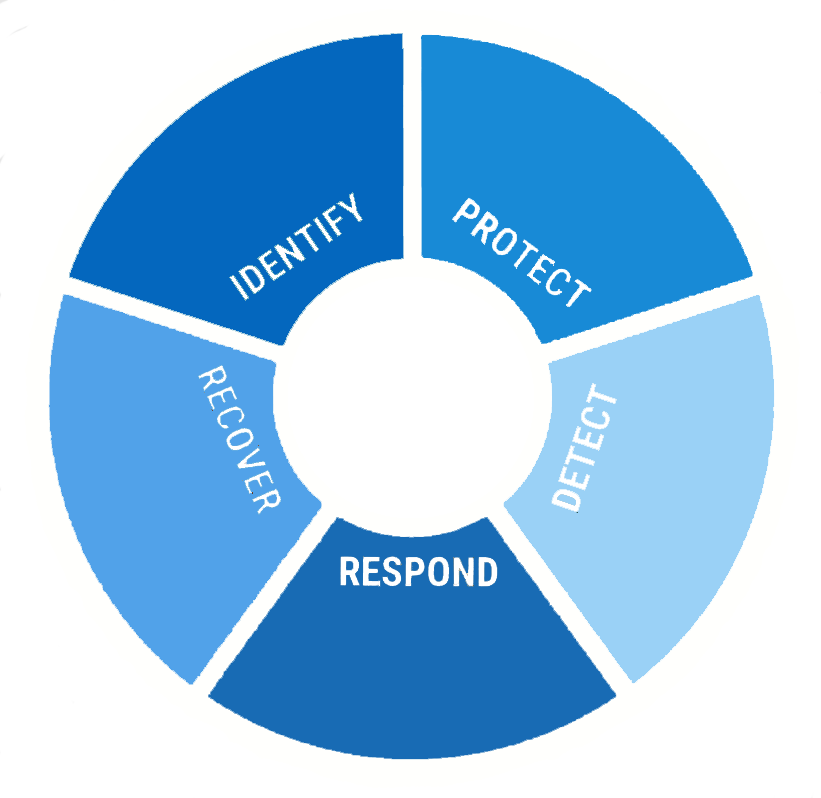
With our security consulting, we’ll assess your network, deploy state-of-the-art security tools, monitor security updates, and adapt your defences. We’ll identify the vulnerabilities with the most significant potential risk, and fortify them.
We conduct tests, evaluate results, refine your security protocols, and reinforce your defences.
And then we safeguard, evaluate, and fortify again.
And again.
With us, security never stops.
Securing your business starts with staying a step ahead.
There is no one-size-fits-all in cyber security. Each business brings its own challenges and risks. So, each security strategy we craft is custom fit, tailored for your business.
Security must be integral part of your organisation.
Our services are key to aligning your IT infrastructure with your business goals, ensuring that your digital assets stay safe.
With our proactive cyber security services, you are not just protected, but prepared for what’s next.
Cyber threats are evolving, but so are our defences. Techcellence is your shield against potential threats – protecting your data, your systems and giving you greater peace of mind.
Unfortunately, most organisations only discover they’ve fallen victim to a cyber attack when it’s too late. The sooner you take action, the better protected you will be.
If your company has not had a security risk assessment recently consider this a sign to act. We recommend getting a professional security assessment as soon as possible.

Starting with a few short questions, we'll provide you an in-depth analysis to help identify and eliminate the gaps in your security, cover vulnerabilities, and build a plan that enables you to respond to future attacks.
Ready to get started?
 |
